Top-Level Takeaways
-
The ACET became part of the examination process in 2018 and includes nearly 500 questions.
-
Compliance vendors are stepping in to aid with process and documentation tracking tools.

Pam Perdue, Executive Vice President and Chief Regulatory Officer, Continuity
The NCUA is now using its own version of the cybersecurity exam required of all financial institutions, and the homework for credit unions ahead of examiner visits can be a doozy.
Called the Automated Cybersecurity Examination Tool, the ACET requires credit unions to answer 494 questions in the form of declarative statements and submit approximately 200 documents for examiners to assess how the institution is preventing and preparing for cyber threats and attacks.
The ACET is based on the Cybersecurity Assessment Tool from the Federal Financial Institutions Examination Council. According to the NCUA, the new exam tool provides a repeatable, measurable, and transparent process that improves and standardizes our supervision related to cybersecurity in all federally insured credit unions.
Its also a lot of work.

Heather McCalman, Credit Union Council Manager, FS-ISAC
Most of our credit union clients report cybersecurity compliance efforts cost them hundreds of hours and tens of thousands of dollars each year, says Pam Perdue, executive vice president and chief regulatory officer at Continuity, a provider of compliance software and consulting solutions. Billion-dollar credit unions can find those costs running into six figures annually.
And the lift isnt much easier for smaller institutions, says Heather McCalman, credit union council manager for FS-ISAC, the financial services industry security consortium.
That number of declarative statements and the depth of some of the statements may sometimes overwhelm a small institutions staff, McCalman says.
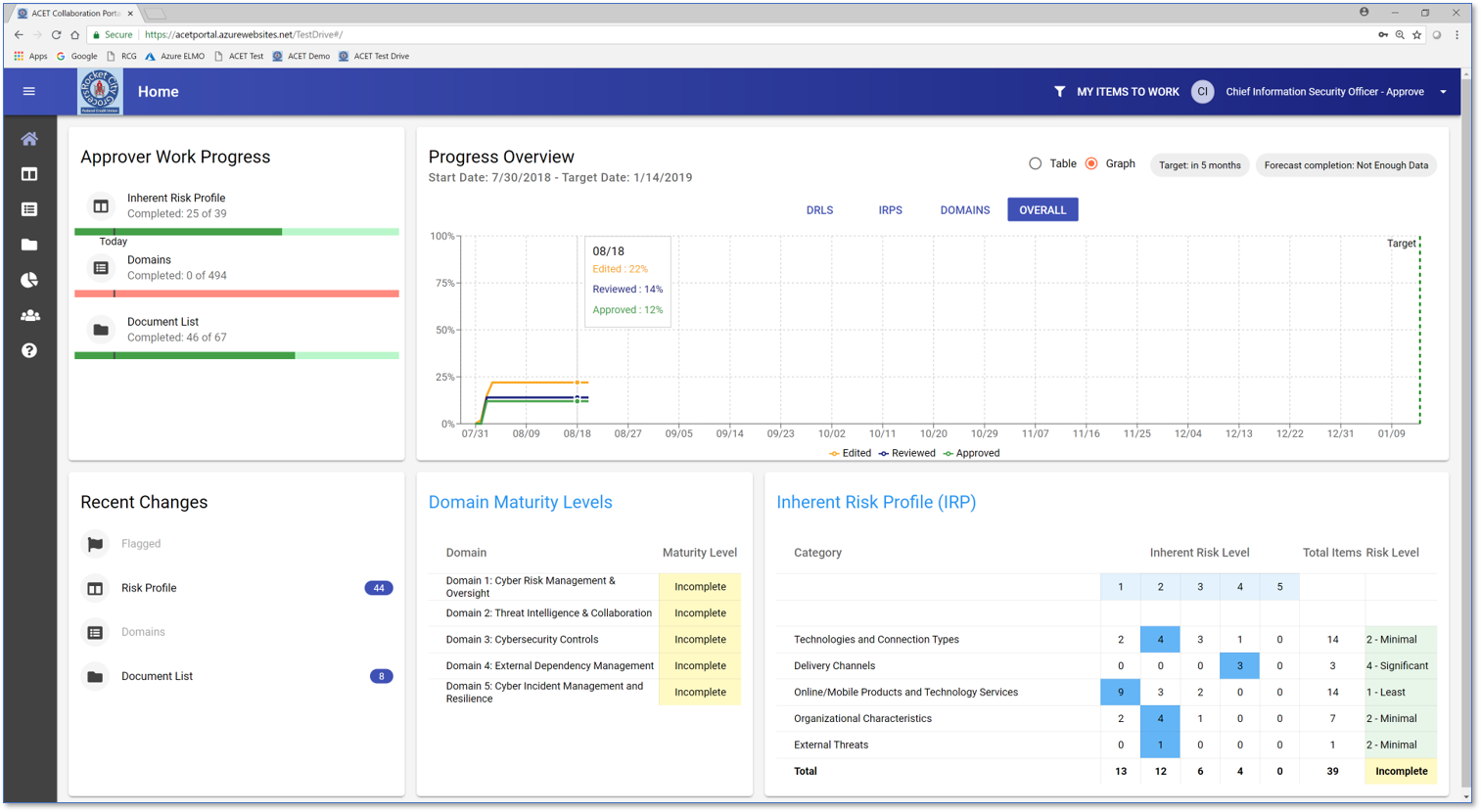
The Redstone Consulting Groups ACT tool helps credit unions organize and execute compliance with the 494-question ACET. To enlarge the image, click .

Jim Bray, Senior Vice President of Business Development, Redstone Consulting Group
RCG is targeting the portal to credit unions of $250 million or more in assets and built the solution based on the big Alabama credit unions own experience with cybersecurity compliance.
Were talking hundreds and thousands of hours going over documents, says Jim Bray, RCGs senior vice president of business development. [Thats] an incredibly manpower-intensive process.
The ACET itself is built as an Excel spreadsheet that measures 39 credit union activities and products through the lens of two major components. The Inherent Risk Profile determines a credit unions exposure to risk by identifying the type, volume, and complexity of the institutions operations. The Cybersecurity Maturity portion measures a credit unions level of risk and corresponding controls.
3 Tips For The Tool
Pam Perdue, chief regulatory officer at Continuity, offers three best practices to ace the ACET exam.
- Divide and conquer. With 494 areas to evaluate, this process can not be done effectively by one person. Distribute the tasks in a sensible way across the organization so everyone understands and embraces the importance of the evaluation process.
- Start early, change often. Risk mitigation is a dynamic process, not a point-in-time approach. Update the program whenever guidelines, internal conditions, or outside threats change to ensure the program is never outdated and the framework is always serving the credit union in the most relevant ways.
- Know when to surrender. Cybersecurity is complicated and requires a highly specialized skill set to manage. If the changing rules and threatscape are outside a credit unions internal capability or capacity to handle, then it should seek outside help from experienced, established, and reputable third parties.
Theres no shame in doing what’s in the best interest of members, Perdue says. Sometimes that means getting help where help is needed.
Without a centralized shared work platform, credit unions had to gather all the relevant personnel in the same room to collaborate on answers, Bray says. RCG build the portal so collaboration could take place outside that room. It eliminates the use of multiple spreadsheets, Word documents, and emails and instead relys on dashboards and a single version control mechanism. For document storage, credit unions can use VirtualStrongbox.
Continuity, meanwhile, offers a compliance management platform that includes ACET functionality in an IT controls environment that also includes regulatory alerts and automatic program updates as the rules change.
Find your next partner in Callahans online Buyer’s Guide. Browse hundreds of supplier profiles by name, keyword, or service area.
McCalman, who joined FS-ISAC after a decade of IT and cybersecurity experience with a South Carolina credit union, says third-party solutions can help organize and control the ACET process for visiting regulators, but they cant totally replace the credit unions involvement in the process.
They wont nor can they answer all the declarative statements, McCalman says. Credit union staff know their systems and network the best. They need to be involved in completing the ACET. Staff members still have to go through all 494 declarative statements, whether its with the ACET in electronic spreadsheet format or with the ACET in a program.
And those staff members also need to know what theyre doing.
Have someone from the IS or IT department involved, McCalman advises. If you dont have that, bring in your virtual CISO, managed security services provider, or other technology consultant to sit with the most tech-savvy person you have.
As comfort, McCalman adds, credit unions only need to complete much of the work once.
When its complete, staff can use the first one as a springboard, she says. The ACET is a living document that should change when new products and services are offered and new security technologies are deployed.
ContentMiddleAd